Every morning, executives worldwide face the same frustrating reality: even after investing millions in customer data platforms and analytics tools, many businesses still operate blind when it comes to understanding customers. The problem isn’t a lack of data — it’s failing to treat identity data as strategic infrastructure (not just a compliance checkbox).
Most businesses collect identity data but fail to unlock its strategic potential:
- Customer information lives in fragmented systems.
- Verification fees get paid repeatedly.
- Customers face high-friction onboarding and re-verification.
- The outcome is lost revenue and lost trust.
We are excited to share how the right approach to identity data eliminates operational inefficiencies while creating seamless customer experiences. The breakthrough is portable identity infrastructure that lets customers verify once and access services everywhere, without businesses storing sensitive personally identifiable information (PII). For more context on AIR, visit air3.com.
Why Traditional Personally Identifiable Information Systems Keep Failing
The fundamental flaw with conventional identity management isn’t technical—it’s architectural. When businesses store personally identifiable information in centralized databases, they create security vulnerabilities, compliance nightmares, and operational inefficiencies that scale with growth.
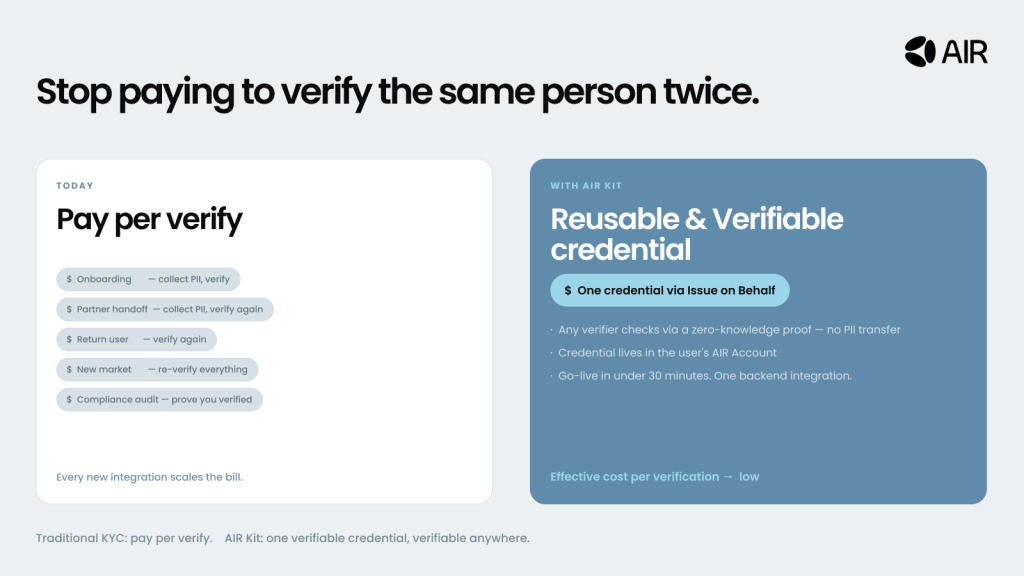
Traditional KYC providers often charge per verification because their business model depends on re-verification:
- Customers switching devices or returning later may have to repeat KYC.
- Businesses pay multiple times for the same customer.
- Customers experience redundant friction.
- Meanwhile, centralized PII storage increases breach risk and reputational damage.
The fragmentation extends beyond verification and hurts the full customer journey:
- Customer service can’t see complete histories.
- Identity systems don’t connect cleanly with loyalty platforms or transaction systems.
- Each silo adds authentication steps, creating extra friction.
- Support volume grows (password resets, account recovery, repeat verification).
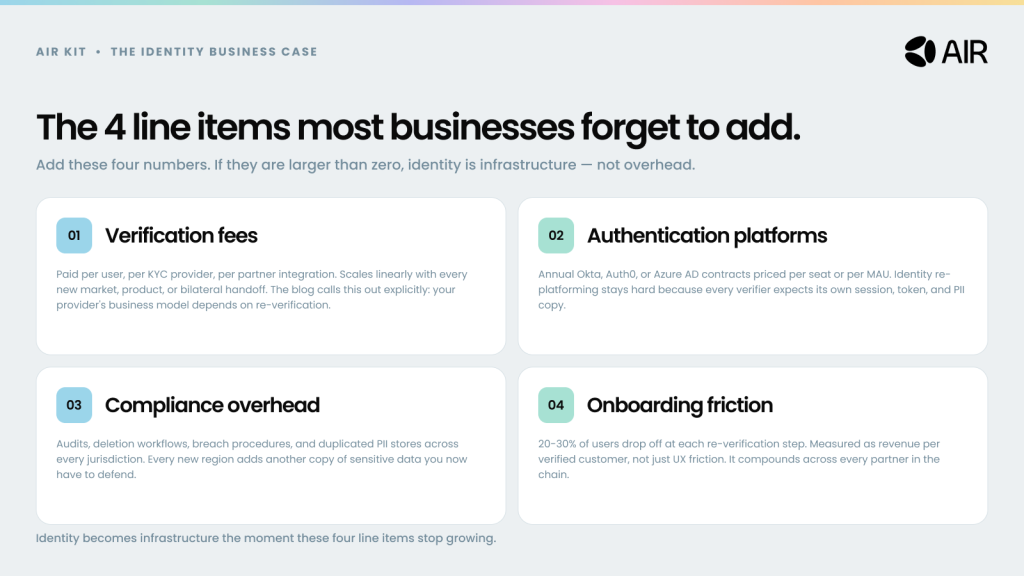
The hidden costs of poor PII and identity data management add up quickly:
- Marketing: weaker personalization because identities don’t connect reliably across channels.
- Sales: lost qualified leads due to long verification and onboarding flows.
- Compliance & security: expanding burden with every new market and integration (audits, breach procedures, deletion workflows, and duplicated sensitive data stores).
How AIR Identity Infrastructure Eliminates PII Data Storage Risks
AIR identity infrastructure represents a shift in how businesses approach customer identity:
- Instead of storing customer data, you issue verifiable credentials that customers carry in their own AIR Account.
- These credentials can prove identity, purchase history, or loyalty status without exposing underlying personally identifiable information.
The architecture solves multiple problems simultaneously. When customers complete verification once, they receive credentials that work across your entire ecosystem and partner network. No re-verification, no redundant data storage, no compliance headaches from PII data sitting in multiple databases. The credential proves they completed verification without revealing actual identity documents or personal information.
Silent credential issuance changes the user experience:
- Backend systems trigger credential creation automatically (purchase completed, loyalty tier reached, verification finished).
- Customers don’t fill extra forms or take additional steps.
- Credentials appear in the AIR Account, ready to unlock benefits across your platform and partner ecosystem.
We are proud to see how companies implementing this approach achieve remarkable results. Customer onboarding times drop from minutes to seconds. Support ticket volumes decrease as password resets become unnecessary. Marketing campaigns achieve higher conversion rates because personalization is based on verified, comprehensive customer profiles rather than fragmented data points.
The verification process works seamlessly across platforms. When customers need to prove they completed KYC, hold VIP status, or own specific products, they present verifiable credentials. Your systems confirm authenticity through cryptographic verification without touching underlying PII data. The entire verification happens in seconds without storing any customer information.
Zero-knowledge proofs enable privacy-preserving verification:
- Prove someone is over 21 without revealing a birthdate.
- Demonstrate premium loyalty status without disclosing full purchase history.
- Confirm accredited investor status without exposing sensitive financial details.
This unlocks privacy-by-design use cases that are difficult to support with centralized identity systems.
Building Strategic Data Identity Infrastructure
Using identity strategically is what separates leaders from followers. The best implementations do two things: remove friction for customers, and create network effects that get stronger over time.
What changes when identity data becomes reusable
- Customers verify once, then reuse that proof across experiences.
- Businesses reduce repeat verification fees and support overhead.
- Security improves because less sensitive data is stored in more places.
The economics improve
Instead of paying per verification to providers, you issue credentials once from your existing KYC provider webhooks. Those credentials can be verified anywhere in the ecosystem, which drives the effective cost per verification toward zero while improving the customer experience.
Implementation is lightweight
Your KYC provider, loyalty platform, or transaction systems already create identity events. You add simple webhook and REST API calls to issue credentials that appear silently in customer AIR Accounts.
For most use cases, setup takes under 30 minutes. No mobile app changes, website changes, or customer communications are required.
What it enables
- Instant cross-platform access after a single verification.
- Faster onboarding to new products.
- Partner verification in seconds.
- Cross-brand loyalty, without linking accounts or sharing personal information.
Your Competitive Advantage Starts Now
The companies that will dominate digital commerce are those recognizing identity infrastructure as strategic differentiation rather than operational overhead. Portable credential infrastructure delivers proven results: reduced operational costs, improved customer satisfaction, enhanced security posture, and sustainable competitive advantages.
The opportunity is particularly significant for businesses willing to move beyond traditional identity management approaches. While competitors struggle with fragmented customer data and compliance complexity, forward-thinking companies build identity systems that create value for customers and businesses simultaneously.
We are excited to see how businesses across industries transform customer relationships through proper identity data implementation. The technical capabilities exist today to implement sophisticated identity strategies that seemed impossible just years ago. Portable credentials, zero-knowledge proofs, and cross-platform verification are proven solutions that leading businesses use to create competitive advantages.
Your next step is evaluating identity costs and friction points:
- Spending on verification systems
- Spending on authentication platforms
- Compliance and security overhead
- Where customers abandon due to verification friction
These inputs help build a clear business case for identity infrastructure investment with measurable results and long-term scalability.
The question isn’t whether identity data will become central to business strategy—it’s whether your business will lead this transformation or struggle to catch up. The companies that act now will define the standards others follow.
Learn more about the ecosystem:
- Website: moca.network
- Documentation: docs.moca.network
- AIR stack: air3.com | Contact us